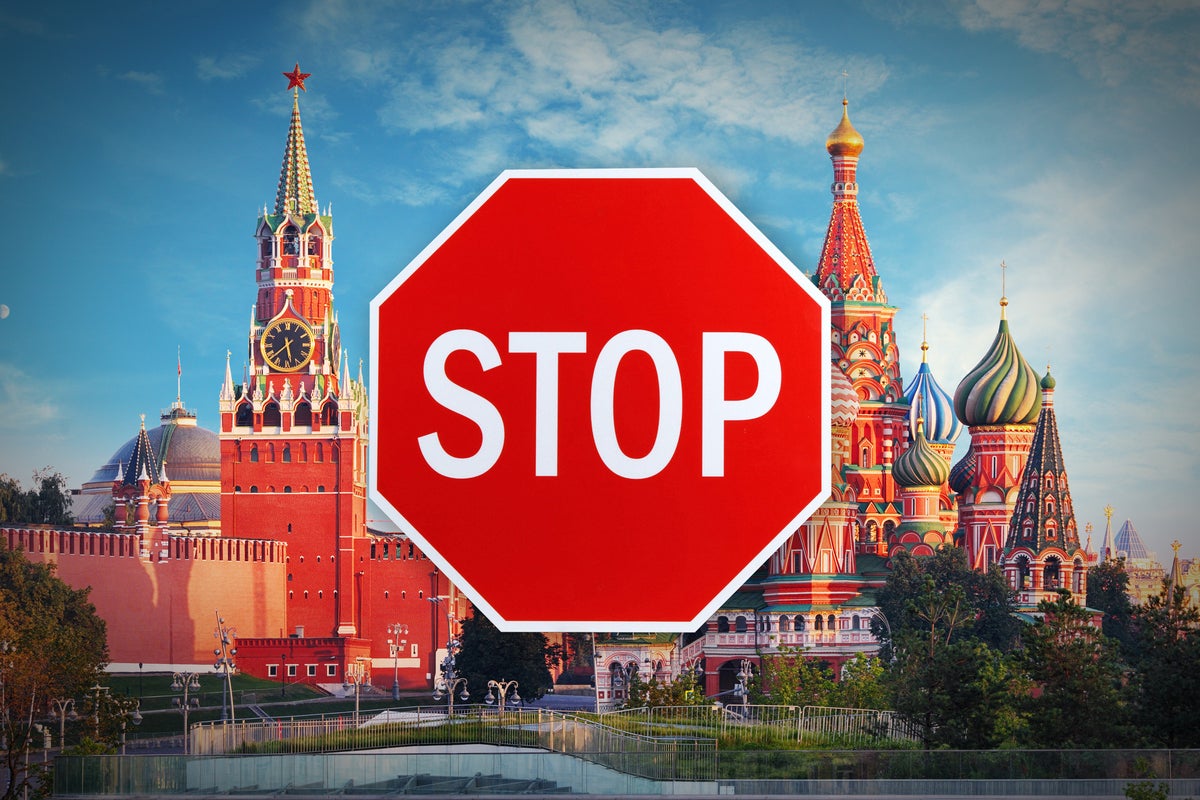
Russia is losing the cyberwar against Ukraine, too
Credit to Author: Preston Gralla| Date: Mon, 02 May 2022 03:00:00 -0700
When Russia launched its all-out attack against Ukraine in February, the world expected the invaders to roll over the country quickly. That didn’t happen, and Ukraine today, though still under assault, has so far thwarted Russia’s ambitions to conquer it.
Russia has also been fighting a quieter war against Ukraine, a cyberwar, deploying what had been considered the most feared state-sponsored hackers in the world. And in the same way that Ukraine has fended off Russia’s military might, it’s been winning the cyberwar as well.
In that cyberwar, as always, the terrain is primarily Windows, because it represents the largest and most vulnerable attack surface in the world. The facts about what exactly is going on have been shadowy. But there’s plenty of evidence that Ukraine may keep the upper hand.