Malicious meeting invite fix targets Mac users
Cybercriminals are targeting Mac users interested in cryptocurrency opportunities with fake calendar invites. During the attacks the criminals will send a link supposedly to add a meeting to the target’s calendar. In reality the link runs a script to install Mac malware on the target’s machine.
Cybersecurity expert Brian Krebs investigated and flagged the issue.
Scammers, impersonating cryptocurrency investors, are active on Telegram channels to get interested people to attend a meeting about a future partnership.
One of those investors called Signum Capital tweeted a warning on X in January that one of their team members was being impersonated on Telegram and sending out invites by direct message (DM).
The criminals reach out to targets by DM on Telegram and ask if they have an interest in hearing more about the opportunity in a call or meeting. If they show interest they will be sent a fabricated invitation for a meeting. When the times comes to join the meeting the invitation link doesn’t work. The scammers tell the victim it’s a known issue, caused by a regional access restriction, which can be solved by running a script.
We asked Malwarebytes Director of Core Technology and resident Apple expert Thomas Reed to look at this method. This isn’t the first time criminals have used scripts to compromise users, he told us.
“AppleScript has been used against Mac users with moderate frequency by malware creators over the years. It has the advantage of being very easy to write, and if compiled, is also extremely difficult to reverse engineer.”AppleScript has been used against Mac users with moderate frequency by malware creators over the years. It has the advantage of being very easy to write, and if compiled, is also extremely difficult to reverse engineer.”
According to Reed, AppleScripts can be provided in a few different forms. One is a simple .scpt file that opens in Apple’s Script Editor app. This has a few drawbacks for criminals: A victim would need to click something within Script Editor to run the script, and they would able to see the code, which might be a problem because AppleScript tends to be more human readable than most other scripts. However, there are ways to obfuscate what the code is doing, and many users won’t bother to read it anyway.
Another option is an AppleScript applet. This is something that acts like a normal Mac app. It contains a basic AppleScript executable and the script to be run. In this form, the script can be code signed, notarized, given an icon, and otherwise made to appear more trustworthy. The code could be pretty bland, and unlikely to trigger any kind of detection from Apple’s notarization process, but could download and execute something less trustworthy.
Scripts have another advantage for criminals, Reed warned.
“AppleScripts also have the advantage of being able to very easily get administrator permissions.”
A script that attempts to run a command with administrator privileges will ask users to authenticate, triggering a password dialog.
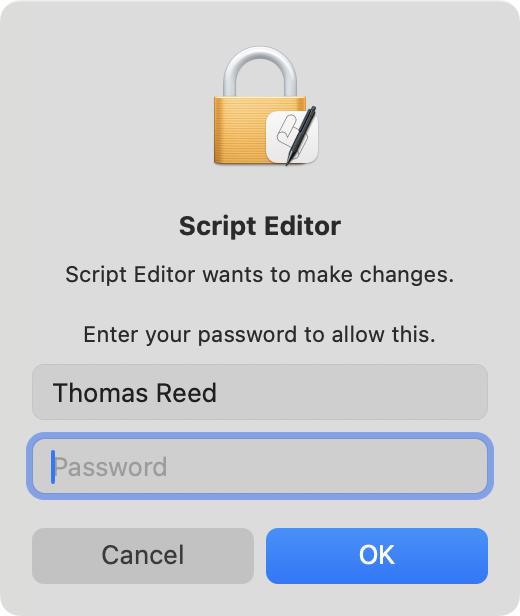
If the user enters their password, the script doesn’t actually get to see it, but everything else the script attempts to do “with administrator privileges” will successfully run as root without further authentication. This makes it very easy for the script to show a standard authentication request dialog and trick the user into giving root permissions.
“So, in summary, AppleScript can be quite effective for writing malware. In fact, some malware has been written exclusively – or almost exclusively – in AppleScript, such as OSX.DubRobber or OSX.OSAMiner.”
In this case, the script was a simple Apple Script that downloaded and executed a macOS-oriented Trojan. The nature of the Trojan is unknown, but it certainly won’t surprise anyone if it turns out it was a banking Trojan that specializes in stealing cryptocurrencies.
Recognizing the scam
To avoid falling victim to these scammers, it’s good to know a few of their tactics.
- Targets are approached by DM on Telegram.
- Topics are cryptocurrency investment opportunities.
- The scammers have a preference for the Calendly scheduling platform.
- A fake “regional access restriction” creates a sense of last minute urgency.
- The script had the
.scpt(Apple script) extension. - The script was hosted on a domain that pretended to be a meeting support site.
The presence of Mac malware is unfortunately still underestimated, but you can find protection by Malwarebytes for Mac and protect Mac endpoints in your environment by ThreatDown solutions.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.