Google patches actively exploited zero-day in Chrome. Update now!
Google has released an update for its Chrome browser which includes a patch for a vulnerability that Google says is already being exploited, known as a zero-day vulnerability.
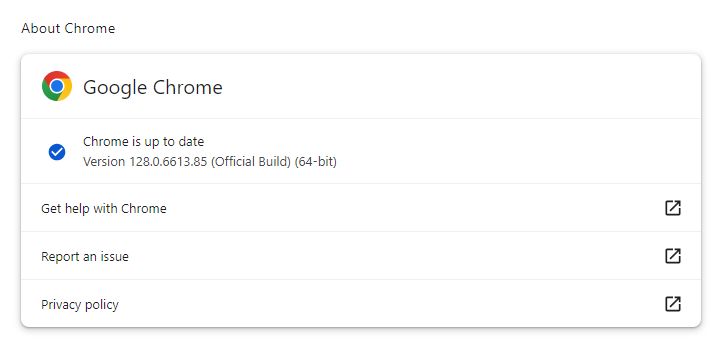
Google has fixed that zero-day with the release of versions 128.0.6613.84/.85 for Windows/macOS and 128.0.6613.84 for Linux that will be rolled out to all users over the coming weeks.
The easiest way to update Chrome is to allow it to update automatically, but you can end up lagging behind if you never close your browser or if something goes wrong—such as an extension stopping you from updating the browser.
To manually get the update, click Settings > About Chrome. If there is an update available, Chrome will notify you and start downloading it. Then all you have to do is restart the browser in order for the update to complete, and for you to be safe from those vulnerabilities.
Besides the zero-day, this update contains 37 other security fixes, as well as Google Lens for desktop. This means you’ll be able to search anything you see on the web without leaving your current tab.
Google Lens will be available on every open tab. Here’s how to use it:
- Open the Chrome menu (three stacked dots).
- Select Search with Google Lens .
- Select anything on the page by clicking and dragging anywhere on the page.
- Refine the answers by typing in the search box in the side panel.
Keep in mind though that Google will receive a screenshot of every Google Lens search you do.
Technical details on the zero-day vulnerability
A zero-day is a vulnerability in software or hardware that is typically unknown to the vendor and for which no patch or other fix is available. The zero-day vulnerability which is being fixed here is referred to as CVE-2024-7971: a type confusion in V8 in Google Chrome which allowed a remote attacker to exploit heap corruption via a crafted HTML page.
JavaScript uses dynamic typing which means the type of a variable is determined and updated at runtime, as opposed to being set at compile-time in a statically typed language.
V8 is the JavaScript engine that Chrome uses and has been a significant source of security problems.
Heap corruption occurs when a program modifies the contents of a memory location outside of the memory allocated to the program. The outcome can be relatively benign and cause a memory leak, or it may be fatal and cause a memory fault, usually in the program that causes the corruption.
So, an attacker will have to convince a target to open a specially crafted HTML file, which usually means visiting a website. This will cause the unpatched browser to accept an unexpected value for a variable that will cause an overflow of the reserved memory location. The attacker is able to abuse that overflow for their own malicious purposes.
We don’t just report on vulnerabilities—we identify them, and prioritize action.
Cybersecurity risks should never spread beyond a headline. Keep vulnerabilities in tow by using ThreatDown Vulnerability and Patch Management.
https://blog.malwarebytes.com/feed/