Windows Security best practices for integrating and managing security tools
Credit to Author: David Weston| Date: Sat, 27 Jul 2024 22:24:03 +0000
Windows is an open and flexible platform used by many of the world’s top businesses for high availability use cases where security and availability are non-negotiable.
To meet those needs:
- Windows provides a range of operating modes that customers can choose from. This includes the ability to limit what can run to only approved software and drivers. This can increase security and reliability by making Windows operate in a mode closer to mobile phones or appliances.
- Customers can choose integrated security monitoring and detection capabilities that are included with Windows. Or they can choose to replace or supplement this security with a wide variety of choices from a vibrant open ecosystem of vendors.
In this blog post, we examine the recent CrowdStrike outage and provide a technical overview of the root cause. We also explain why security products use kernel-mode drivers today and the safety measures Windows provides for third-party solutions. In addition, we share how customers and security vendors can better leverage the integrated security capabilities of Windows for increased security and reliability. Lastly, we provide a look into how Windows will enhance extensibility for future security products.
CrowdStrike recently published a Preliminary Post Incident Review analyzing their outage. In their blog post, CrowdStrike describes the root cause as a memory safety issue—specifically a read out-of-bounds access violation in the CSagent driver. We leverage the Microsoft WinDBG Kernel Debugger and several extensions that are available free to anyone to perform this analysis. Customers with crash dumps can reproduce our steps with these tools.
Based on Microsoft’s analysis of the Windows Error Reporting (WER) kernel crash dumps related to the incident, we observe global crash patterns that reflect this:
FAULTING_THREAD: ffffe402fe868040 READ_ADDRESS: ffff840500000074 Paged pool MM_INTERNAL_CODE: 2 IMAGE_NAME: csagent.sys MODULE_NAME: csagent FAULTING_MODULE: fffff80671430000 csagent PROCESS_NAME: System TRAP_FRAME: ffff94058305ec20 -- (.trap 0xffff94058305ec20) .trap 0xffff94058305ec20 NOTE: The trap frame does not contain all registers. Some register values may be zeroed or incorrect. rax=ffff94058305f200 rbx=0000000000000000 rcx=0000000000000003 rdx=ffff94058305f1d0 rsi=0000000000000000 rdi=0000000000000000 rip=fffff806715114ed rsp=ffff94058305edb0 rbp=ffff94058305eeb0 r8=ffff840500000074 r9=0000000000000000 r10=0000000000000000 r11=0000000000000014 r12=0000000000000000 r13=0000000000000000 r14=0000000000000000 r15=0000000000000000 iopl=0 nv up ei ng nz na po nc csagent+0xe14ed: fffff806`715114ed 458b08 mov r9d,dword ptr [r8] ds:ffff8405`00000074=???????? .trap Resetting default scope STACK_TEXT: ffff9405`8305e9f8 fffff806`5388c1e4 : 00000000`00000050 ffff8405`00000074 00000000`00000000 ffff9405`8305ec20 : nt!KeBugCheckEx ffff9405`8305ea00 fffff806`53662d8c : 00000000`00000000 00000000`00000000 00000000`00000000 ffff8405`00000074 : nt!MiSystemFault+0x1fcf94 ffff9405`8305eb00 fffff806`53827529 : ffffffff`00000030 ffff8405`af8351a2 ffff9405`8305f020 ffff9405`8305f020 : nt!MmAccessFault+0x29c ffff9405`8305ec20 fffff806`715114ed : 00000000`00000000 ffff9405`8305eeb0 ffff8405`b0bcd00c ffff8405`b0bc505c : nt!KiPageFault+0x369 ffff9405`8305edb0 fffff806`714e709e : 00000000`00000000 00000000`e01f008d ffff9405`8305f102 fffff806`716baaf8 : csagent+0xe14ed ffff9405`8305ef50 fffff806`714e8335 : 00000000`00000000 00000000`00000010 00000000`00000002 ffff8405`b0bc501c : csagent+0xb709e ffff9405`8305f080 fffff806`717220c7 : 00000000`00000000 00000000`00000000 ffff9405`8305f382 00000000`00000000 : csagent+0xb8335 ffff9405`8305f1b0 fffff806`7171ec44 : ffff9405`8305f668 fffff806`53eac2b0 ffff8405`afad4ac0 00000000`00000003 : csagent+0x2f20c7 ffff9405`8305f430 fffff806`71497a31 : 00000000`0000303b ffff9405`8305f6f0 ffff8405`afb1d140 ffffe402`ff251098 : csagent+0x2eec44 ffff9405`8305f5f0 fffff806`71496aee : ffff8405`afb1d140 fffff806`71541e7e 00000000`000067a0 fffff806`7168f8f0 : csagent+0x67a31 ffff9405`8305f760 fffff806`7149685b : ffff9405`8305f9d8 ffff8405`afb1d230 ffff8405`afb1d140 ffffe402`fe8644f8 : csagent+0x66aee ffff9405`8305f7d0 fffff806`715399ea : 00000000`4a8415aa ffff8eee`1c68ca4f 00000000`00000000 ffff8405`9e95fc30 : csagent+0x6685b ffff9405`8305f850 fffff806`7148efbb : 00000000`00000000 ffff9405`8305fa59 ffffe402`fe864050 ffffe402`fede62c0 : csagent+0x1099ea ffff9405`8305f980 fffff806`7148edd7 : ffffffff`ffffffa1 fffff806`7152e5c1 ffffe402`fe864050 00000000`00000001 : csagent+0x5efbb ffff9405`8305fac0 fffff806`7152e681 : 00000000`00000000 fffff806`53789272 00000000`00000002 ffffe402`fede62c0 : csagent+0x5edd7 ffff9405`8305faf0 fffff806`53707287 : ffffe402`fe868040 00000000`00000080 fffff806`7152e510 006fe47f`b19bbdff : csagent+0xfe681 ffff9405`8305fb30 fffff806`5381b8e4 : ffff9680`37651180 ffffe402`fe868040 fffff806`53707230 00000000`00000000 : nt!PspSystemThreadStartup+0x57 ffff9405`8305fb80 00000000`00000000 : ffff9405`83060000 ffff9405`83059000 00000000`00000000 00000000`00000000 : nt!KiStartSystemThread+0x34 Digging in more to this crash dump, we can restore the stack frame at the time of the access violation to learn more about its origin. Unfortunately, with WER data we only receive a compressed version of state and thus we cannot disassemble backwards to see a larger set of instructions prior to the crash, but we can see in the disassembly that there is a check for NULL before performing a read at the address specified in the R8 register:
6: kd> .trap 0xffff94058305ec20 .trap 0xffff94058305ec20 NOTE: The trap frame does not contain all registers. Some register values may be zeroed or incorrect. rax=ffff94058305f200 rbx=0000000000000000 rcx=0000000000000003 rdx=ffff94058305f1d0 rsi=0000000000000000 rdi=0000000000000000 rip=fffff806715114ed rsp=ffff94058305edb0 rbp=ffff94058305eeb0 r8=ffff840500000074 r9=0000000000000000 r10=0000000000000000 r11=0000000000000014 r12=0000000000000000 r13=0000000000000000 r14=0000000000000000 r15=000000000000 000 iopl=0 nv up ei ng nz na po nc csagent+0xe14ed: fffff806`715114ed 458b08 mov r9d,dword ptr [r8] ds:ffff8405`00000074=???????? 6: kd> !pte ffff840500000074 !pte ffff840500000074 VA ffff840500000074 PXE at FFFFABD5EAF57840 PPE at FFFFABD5EAF080A0 PDE at FFFFABD5E1014000 PTE at FFFFABC202800000 contains 0A00000277200863 contains 0000000000000000 pfn 277200 ---DA--KWEV contains 0000000000000000 not valid 6: kd> ub fffff806`715114ed ub fffff806`715114ed csagent+0xe14d9: fffff806`715114d9 04d8 add al,0D8h fffff806`715114db 750b jne csagent+0xe14e8 (fffff806`715114e8) fffff806`715114dd 4d85c0 test r8,r8 fffff806`715114e0 7412 je csagent+0xe14f4 (fffff806`715114f4) fffff806`715114e2 450fb708 movzx r9d,word ptr [r8] fffff806`715114e6 eb08 jmp csagent+0xe14f0 (fffff806`715114f0) fffff806`715114e8 4d85c0 test r8,r8 fffff806`715114eb 7407 je csagent+0xe14f4 (fffff806`715114f4) 6: kd> ub fffff806`715114d9 ub fffff806`715114d9 ^ Unable to find valid previous instruction for 'ub fffff806`715114d9' 6: kd> u fffff806`715114eb u fffff806`715114eb csagent+0xe14eb: fffff806`715114eb 7407 je csagent+0xe14f4 (fffff806`715114f4) fffff806`715114ed 458b08 mov r9d,dword ptr [r8] fffff806`715114f0 4d8b5008 mov r10,qword ptr [r8+8] fffff806`715114f4 4d8bc2 mov r8,r10 fffff806`715114f7 488d4d90 lea rcx,[rbp-70h] fffff806`715114fb 488bd6 mov rdx,rsi fffff806`715114fe e8212c0000 call csagent+0xe4124 (fffff806`71514124) fffff806`71511503 4533d2 xor r10d,r10d 6: kd> db ffff840500000074 db ffff840500000074 ffff8405`00000074 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`00000084 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`00000094 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`000000a4 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`000000b4 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`000000c4 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`000000d4 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? ffff8405`000000e4 ?? ?? ?? ?? ?? ?? ?? ??-?? ?? ?? ?? ?? ?? ?? ?? ???????????????? Our observations confirm CrowdStrike’s analysis that this was a read-out-of-bounds memory safety error in the CrowdStrike developed CSagent.sys driver.
We can also see that the csagent.sys module is registered as a file system filter driver commonly used by anti-malware agents to receive notifications about file operations such as the creation or modification of a file. This is often used by security products to scan any new file saved to disk, such as downloading a file via the browser.
File System filters can also be used as a signal for security solutions attempting to monitor the behavior of the system. CrowdStrike noted in their blog that part of their content update was changing the sensor’s logic relating to data around named pipe creation. The File System filter driver API allows the driver to receive a call when named pipe activity (e.g., named pipe creation) occurs on the system that could enable the detection of malicious behavior. The general function of the driver correlates to the information shared by CrowdStrike.
6: kd>!reg querykey REGISTRYMACHINEsystemControlSet001servicescsagent Hive ffff84059ca7b000 KeyNode ffff8405a6f67f9c [SubKeyAddr] [SubKeyName] ffff8405a6f683ac Instances ffff8405a6f6854c Sim Use '!reg keyinfo ffff84059ca7b000 <SubKeyAddr>' to dump the subkey details [ValueType] [ValueName] [ValueData] REG_DWORD Type 2 REG_DWORD Start 1 REG_DWORD ErrorControl 1 REG_EXPAND_SZ ImagePath ??C:Windowssystem32driversCrowdStrikecsagent.sys REG_SZ DisplayName CrowdStrike Falcon REG_SZ Group FSFilter Activity Monitor REG_MULTI_SZ DependOnService FltMgr� REG_SZ CNFG Config.sys REG_DWORD SupportedFeatures f We can see the control channel file version 291 specified in the CrowdStrike analysis is also present in the crash indicating the file was read.
Determining how the file itself correlates to the access violation observed in the crash dump would require additional debugging of the driver using these tools but is outside of the scope of this blog post.
!ca ffffde8a870a8290 ControlArea @ ffffde8a870a8290 Segment ffff880ce0689c10 Flink ffffde8a87267718 Blink ffffde8a870a7d98 Section Ref 0 Pfn Ref b Mapped Views 0 User Ref 0 WaitForDel 0 Flush Count 0 File Object ffffde8a879b29a0 ModWriteCount 0 System Views 0 WritableRefs 0 PartitionId 0 Flags (8008080) File WasPurged OnUnusedList WindowsSystem32driversCrowdStrikeC-00000291-00000000-00000032.sys 1: kd> !ntfskd.ccb ffff880ce06f6970 !ntfskd.ccb ffff880ce06f6970 Ccb: ffff880c`e06f6970 Flags: 00008003 Cleanup OpenAsFile IgnoreCase Flags2: 00000841 OpenComplete AccessAffectsOplocks SegmentObjectReferenced Type: UserFileOpen FileObj: ffffde8a879b29a0 (018) ffff880c`db937370 FullFileName [WindowsSystem32driversCrowdStrikeC-00000291-00000000-00000032.sys] (020) 000000000000004C LastFileNameOffset (022) 0000000000000000 EaModificationCount (024) 0000000000000000 NextEaOffset (048) FFFF880CE06F69F8 Lcb (058) 0000000000000002 TypeOfOpen We can leverage the crash dump to determine if any other drivers supplied by CrowdStrike may exist on the running system during the crash.
6: kd> lmDvmCSFirmwareAnalysis lmDvmCSFirmwareAnalysis Browse full module list start end module name fffff806`58920000 fffff806`5893c000 CSFirmwareAnalysis (deferred) Image path: SystemRootsystem32DRIVERSCSFirmwareAnalysis.sys Image name: CSFirmwareAnalysis.sys Browse all global symbols functions data Symbol Reload Timestamp: Mon Mar 18 11:32:14 2024 (65F888AE) CheckSum: 0002020E ImageSize: 0001C000 Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4 Information from resource tables: 6: kd> lmDvmcspcm4 lmDvmcspcm4 Browse full module list start end module name fffff806`71870000 fffff806`7187d000 cspcm4 (deferred) Image path: ??C:Windowssystem32driversCrowdStrikecspcm4.sys Image name: cspcm4.sys Browse all global symbols functions data Symbol Reload Timestamp: Mon Jul 8 18:33:22 2024 (668C9362) CheckSum: 00012F69 ImageSize: 0000D000 Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4 Information from resource tables: 6: kd> lmDvmcsboot.sys lmDvmcsboot.sys Browse full module list start end module name Unloaded modules: fffff806`587d0000 fffff806`587dc000 CSBoot.sys Timestamp: unavailable (00000000) Checksum: 00000000 ImageSize: 0000C000 6: kd> !reg querykey REGISTRYMACHINEsystemControlSet001servicescsboot !reg querykey REGISTRYMACHINEsystemControlSet001servicescsboot Hive ffff84059ca7b000 KeyNode ffff8405a6f68924 [ValueType] [ValueName] [ValueData] REG_DWORD Type 1 REG_DWORD Start 0 REG_DWORD ErrorControl 1 REG_EXPAND_SZ ImagePath system32driversCrowdStrikeCSBoot.sys REG_SZ DisplayName CrowdStrike Falcon Sensor Boot Driver REG_SZ Group Early-Launch 6: kd> !reg querykey REGISTRYMACHINEsystemControlSet001servicescsdevicecontrol !reg querykey REGISTRYMACHINEsystemControlSet001servicescsdevicecontrol Hive ffff84059ca7b000 KeyNode ffff8405a6f694ac [SubKeyAddr] [VolatileSubKeyName] ffff84059ce196c4 Enum Use '!reg keyinfo ffff84059ca7b000 <SubKeyAddr>' to dump the subkey details [ValueType] [ValueName] [ValueData] REG_DWORD Type 1 REG_DWORD Start 3 REG_DWORD ErrorControl 1 REG_DWORD Tag 1f REG_EXPAND_SZ ImagePath SystemRootSystem32driversCSDeviceControl.sys REG_SZ DisplayName @oem40.inf,%DeviceControl.SVCDESC%;CrowdStrike Device Control Service REG_SZ Group Base REG_MULTI_SZ Owners oem40.inf�!csdevicecontrol.inf_amd64_b6725a84d4688d5a�!csdevicecontrol.inf_amd64_016e965488e83578� REG_DWORD BootFlags 14 6: kd> !reg querykey REGISTRYMACHINEsystemControlSet001servicescsagent !reg querykey REGISTRYMACHINEsystemControlSet001servicescsagent Hive ffff84059ca7b000 KeyNode ffff8405a6f67f9c [SubKeyAddr] [SubKeyName] ffff8405a6f683ac Instances ffff8405a6f6854c Sim Use '!reg keyinfo ffff84059ca7b000 <SubKeyAddr>' to dump the subkey details [ValueType] [ValueName] [ValueData] REG_DWORD Type 2 REG_DWORD Start 1 REG_DWORD ErrorControl 1 REG_EXPAND_SZ ImagePath ??C:Windowssystem32driversCrowdStrikecsagent.sys REG_SZ DisplayName CrowdStrike Falcon REG_SZ Group FSFilter Activity Monitor REG_MULTI_SZ DependOnService FltMgr� REG_SZ CNFG Config.sys REG_DWORD SupportedFeatures f 6: kd> lmDvmCSFirmwareAnalysis lmDvmCSFirmwareAnalysis Browse full module list start end module name fffff806`58920000 fffff806`5893c000 CSFirmwareAnalysis (deferred) Image path: SystemRootsystem32DRIVERSCSFirmwareAnalysis.sys Image name: CSFirmwareAnalysis.sys Browse all global symbols functions data Symbol Reload Timestamp: Mon Mar 18 11:32:14 2024 (65F888AE) CheckSum: 0002020E ImageSize: 0001C000 Translations: 0000.04b0 0000.04e4 0409.04b0 0409.04e4 Information from resource tables: 6: kd> !reg querykey REGISTRYMACHINEsystemControlSet001servicescsfirmwareanalysis !reg querykey REGISTRYMACHINEsystemControlSet001servicescsfirmwareanalysis Hive ffff84059ca7b000 KeyNode ffff8405a6f69d9c [SubKeyAddr] [VolatileSubKeyName] ffff84059ce197cc Enum Use '!reg keyinfo ffff84059ca7b000 <SubKeyAddr>' to dump the subkey details [ValueType] [ValueName] [ValueData] REG_DWORD Type 1 REG_DWORD Start 0 REG_DWORD ErrorControl 1 REG_DWORD Tag 6 REG_EXPAND_SZ ImagePath system32DRIVERSCSFirmwareAnalysis.sys REG_SZ DisplayName @oem43.inf,%FirmwareAnalysis.SVCDESC%;CrowdStrike Firmware Analysis Service REG_SZ Group Boot Bus Extender REG_MULTI_SZ Owners oem43.inf�!csfirmwareanalysis.inf_amd64_12861fc608fb1440� 6: kd> !reg querykey REGISTRYMACHINEsystemControlset001controlearlylaunch !reg querykey REGISTRYMACHINEsystemControlset001controlearlylaunch As we can see from the above analysis, CrowdStrike loads four driver modules. One of those modules receives dynamic control and content updates frequently based on the CrowdStrike Preliminary Post-incident-review timeline.
We can leverage the unique stack and attributes of this crash to identify the Windows crash reports generated by this specific CrowdStrike programming error. It’s worth noting the number of devices which generated crash reports is a subset of the number of impacted devices previously shared by Microsoft in our blog post, because crash reports are sampled and collected only from customers who choose to upload their crashes to Microsoft. Customers who choose to enable crash dump sharing help both driver vendors and Microsoft to identify and remediate quality issues and crashes.
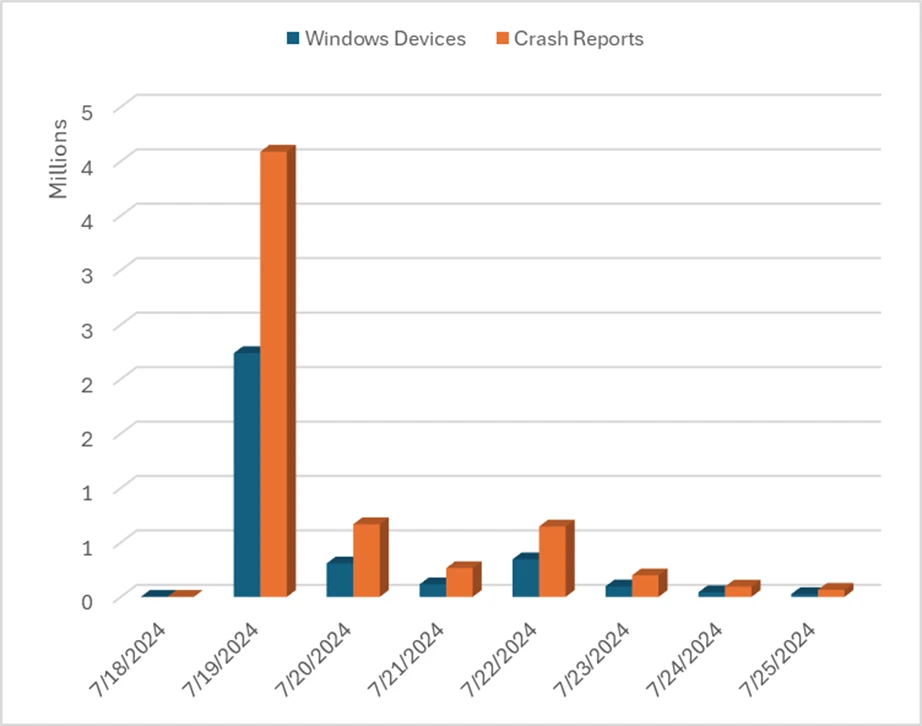
We make this information available to driver owners so they can assess their own reliability via the Hardware Dev Center analytics dashboard. As we can see from the above, any reliability problem like this invalid memory access issue can lead to widespread availability issues when not combined with safe deployment practices. Let’s dig into why security solutions leverage kernel drivers on Windows.
Why do security solutions leverage kernel drivers?
Many security vendors such as CrowdStrike and Microsoft leverage a kernel driver architecture and there are several reasons for this.
Visibility and enforcement of security related events
Kernel drivers allow for system wide visibility, and the capability to load in early boot to detect threats like boot kits and root kits which can load before user-mode applications. In addition, Microsoft provides a rich set of capabilities such as system event callbacks for process and thread creation and filter drivers which can watch for events like file creation, deletion, or modification. Kernel activity can also trigger call backs for drivers to decide when to block activities like file or process creations. Many vendors also use drivers to collect a variety of network information in the kernel using the NDIS driver class.
Performance
Kernel drivers are often utilized by security vendors for potential performance benefits. For example, analysis or data collection for high throughput network activity may benefit from a kernel driver. There are many scenarios where data collection and analysis can be optimized for operation outside of kernel mode and Microsoft continues to partner with the ecosystem to improve performance and provide best practices to achieve parity outside of kernel mode.
Tamper resistance
A second benefit of loading into kernel mode is tamper resistance. Security products want to ensure that their software cannot be disabled by malware, targeted attacks, or malicious insiders, even when those attackers have admin-level privileges. They also want to ensure that their drivers load as early as possible so that they can observe system events at the earliest possible time. Windows provides a mechanism to launch drivers marked as Early Launch Antimalware (ELAM) early in the boot process for this reason. CrowdStrike signs the above CSboot driver as ELAM, enabling it to load early in the boot sequence.
In the general case, there is a tradeoff that security vendors must rationalize when it comes to kernel drivers. Kernel drivers provide the above properties at the cost of resilience. Since kernel drivers run at the most trusted level of Windows, where containment and recovery capabilities are by nature constrained, security vendors must carefully balance needs like visibility and tamper resistance with the risk of operating within kernel mode.
All code operating at kernel level requires extensive validation because it cannot fail and restart like a normal user application. This is universal across all operating systems. Internally at Microsoft, we have invested in moving complex Windows core services from kernel to user mode, such as font file parsing from kernel to user mode.
It is possible today for security tools to balance security and reliability. For example, security vendors can use minimal sensors that run in kernel mode for data collection and enforcement limiting exposure to availability issues. The remainder of the key product functionality includes managing updates, parsing content, and other operations can occur isolated within user mode where recoverability is possible. This demonstrates the best practice of minimizing kernel usage while still maintaining a robust security posture and strong visibility.
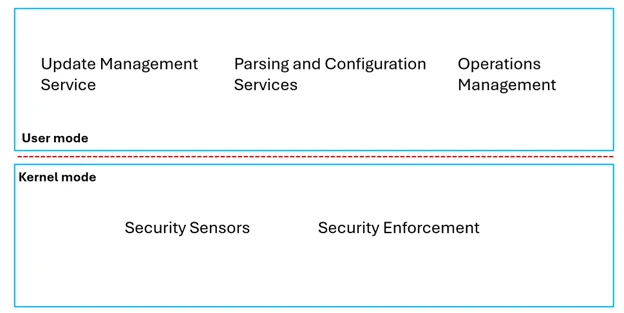
Windows provides several user mode protection approaches for anti-tampering, like Virtualization-based security (VBS) Enclaves and Protected Processes that vendors can use to protect their key security processes. Windows also provides ETW events and user-mode interfaces like Antimalware Scan Interface for event visibility. These robust mechanisms can be used to reduce the amount of kernel code needed to create a security solution, which balances security and robustness.
How does Windows help ensure the quality of security related third-party products?
Microsoft engages with third-party security vendors through an industry forum called the Microsoft Virus Initiative (MVI). This group consists of Microsoft and Security Industry and was created to establish a dialogue and collaboration across the Windows security ecosystem to improve robustness in the way security products use the platform. With MVI, Microsoft and vendors collaborate on the Windows platform to define reliable extension points and platform improvements, as well as share information about how to best protect our customers.
Microsoft works with members of MVI to ensure compatibility with Windows updates, improve performance, and address reliability issues. MVI partners actively participating in the program contribute to making the ecosystem more resilient and gain benefits including technical briefings, feedback loops with Microsoft product teams, and access to antimalware platform features such as ELAM and Protected Processes. Microsoft also provides runtime protection such as Patch Guard to prevent disruptive behavior from kernel driver types like anti-malware.
In addition, all drivers signed by the Microsoft Windows Hardware Quality Labs (WHQL) must run a series of tests and attest to a number of quality checks, including using fuzzers, running static code analysis and testing under runtime driver verification, among other techniques. These tests have been developed to ensure that best practices around security and reliability are followed. Microsoft includes all these tools in the Windows Driver Kit used by all driver developers. A list of the resources and tools is available here.
All WHQL signed drivers are run through Microsoft’s ingestion checks and malware scans and must pass before being approved for signing. Additionally, if a third-party vendor chooses to distribute their driver via Windows Update (WU), the driver also goes through Microsoft’s flighting and gradual rollout processes to observe quality and ensure the driver meets the necessary quality criteria for a broad release.
Can customers deploy Windows in a higher security mode to increase reliability?
Windows at its core is an open and versatile OS, and it can easily be locked down for increased security using integrated tools. In addition, Windows is constantly increasing security defaults, including dozens of new security features enabled by default in Windows 11.
Security features enabled by default in Windows 11
| Area | Feature |
| Hardware Security Baseline | TPM2.0 Secure boot Virtualization-based security (VBS) Memory integrity (Hypervisor-protected Code Integrity (HVCI)) Hardware-enforced stack protection Kernel Direct Memory Access (DMA) protection HW-based kernel protection (HLAT) Enhanced sign-in security (ESS) for built-in biometric sensors |
| Encryption | BitLocker (commercial) Device Encryption (consumer) |
| Identity Management | Credential Guard Entra primary refresh token (PRT) hardware protected MDM deployed SCEP certs hardware protected MDM enrollment certs hardware protected Local Security Authority (LSA) PPL prevents token/credential dumping Account lockout policy (for 10 failed sign-ins) Enhanced phishing protection with Microsoft Defender Microsoft Defender SmartScreen NPLogonNotification doesn’t include password WDigest SSO removed to reduce password disclosure AD Device Account protected by CredGuard* |
| Multi-Factor Authentication (Passwordless) | MSA & Entra users lead through Hello enablement by default MSA password automatically removed from Windows if never used Hello container VSM protected Peripheral biometric sensors blocked for ESS enabled devices Lock on leave integrated into Hello |
| Security Incident Reduction | Common Log File Systems run from trusted source Move tool-tip APIs from kernel to user mode Modernize print stack by removing untrusted drivers DPAPI moved from 3DES to AES TLS 1.3 default with TLS 1.0/1.1 disabled by default NTLM-less* |
| OS lockdown | Microsoft Vulnerable Driver Blocklist 3P driver security baseline enforced via WHCP Smart App Control* |
Windows has integrated security features to self-defend. This includes key anti-malware features enabled by default, such as:
- Secure Boot, which helps prevent early boot malware and rootkits by enforcing signing consistently across Windows boots.
- Measured Boot, which provides TPM-based hardware cryptographic measurements on boot-time properties available through integrated attestation services such as Device Health Attestation.
- Memory integrity (also known as hypervisor-protected code integrity or HVCI), which prevents runtime generation of dynamic code in the kernel and helps ensure control flow integrity.
- Vulnerable driver blocklist, which is on by default, integrated into the OS, and managed by Microsoft. This complements the malicious driver block list.
- Protected Local Security Authority is on by default in Windows 11 to protect a range of credentials. Hardware-based credential protection is on by default for enterprise versions of Windows.
- Microsoft Defender Antivirus is enabled by default in Windows and offers anti-malware capabilities across the OS.
These security capabilities provide layers of protection against malware and exploitation attempts in modern Windows. Many Windows customers have leveraged our security baseline and Windows security technologies to harden their systems and these capabilities collectively have reduced the attack surface significantly.
Using the integrated security features of Windows to prevent adversary attacks such as those displayed in the MITRE ATT&CK® framework increases security while reducing cost and complexity. It leverages best practices to achieve maximum security and reliability. These best practices include:
- Using App Control for Business (formerly Windows Defender Application Control), you can author a security policy to allow only trusted and/or business-critical apps. Your policy can be crafted to deterministically and durably prevent nearly all malware and “living off the land” style attacks. It can also specify which kernel drivers are allowed by your organization to durably guarantee that only those drivers will load on your managed endpoints.
- Use Memory integrity with a specific allow list policy to further protect the Windows kernel using Virtualization-based security (VBS). Combined with App Control for Business, memory integrity can reduce the attack surface for kernel malware or boot kits. This can also be used to limit any drivers that might impact reliability on systems.
- Running as Standard User and elevating only as necessary. Companies that follow the best practices to run as standard user and reduce privileges mitigate many of the MITRE ATT&CK® techniques.
- Use Device Health Attestation (DHA) to monitor devices for the right security policy, including hardware-based measurements for the security posture of the machine. This is a modern and exceptionally durable approach to ensure security for high availability scenarios and uses Microsoft’s Zero Trust architecture.
What is next?
Windows is a self-protecting operating system that has produced dozens of new security features and architectural changes in recent versions. We plan to work with the anti-malware ecosystem to take advantage of these integrated features to modernize their approach, helping to support and even increase security along with reliability.
This includes helping the ecosystem by:
- Providing safe rollout guidance, best practices, and technologies to make it safer to perform updates to security products.
- Reducing the need for kernel drivers to access important security data.
- Providing enhanced isolation and anti-tampering capabilities with technologies like our recently announced VBS enclaves.
- Enabling zero trust approaches like high integrity attestation which provides a method to determine the security state of the machine based on the health of Windows native security features.
As we move forward, Windows is continuing to innovate and offer new ways for security tools to detect and respond to emerging threats safely and securely. Windows has announced a commitment around the Rust programming language as part of Microsoft’s Secure Future Initiative (SFI) and has recently expanded the Windows kernel to support Rust.
The information in this blog post is provided as part of our commitment to communicate learnings and next steps after the CrowdStrike incident. We will continue to share ongoing guidance on security best practices for Windows and work across our broad ecosystem of customers and partners to develop new security capabilities based on your feedback.
The post Windows Security best practices for integrating and managing security tools appeared first on Microsoft Security Blog.