Atomic Stealer distributed to Mac users via fake browser updates
Atomic Stealer, also known as AMOS, is a popular stealer for Mac OS. Back in September, we described how malicious ads were tricking victims into downloading this piece of malware under the disguise of a popular application.
In an interesting new development, AMOS is now being delivered to Mac users via a fake browser update chain tracked as ‘ClearFake’. This may very well be the first time we see one of the main social engineering campaigns, previously reserved for Windows, branch out not only in terms of geolocation but also operating system.
With a growing list of compromised sites at their disposal, the threat actors are able to reach out a wider audience, stealing credentials and files of interest that can be monetized immediately or repurposed for additional attacks.
Discovery
ClearFake is a newer malware campaign that leverages compromised websites to distribute fake browser updates. It was originally discovered by Randy McEoin in August and has since gone through a number of upgrades, including the use of smart contracts to build its redirect mechanism, making it one of the most prevalent and dangerous social engineering schemes.
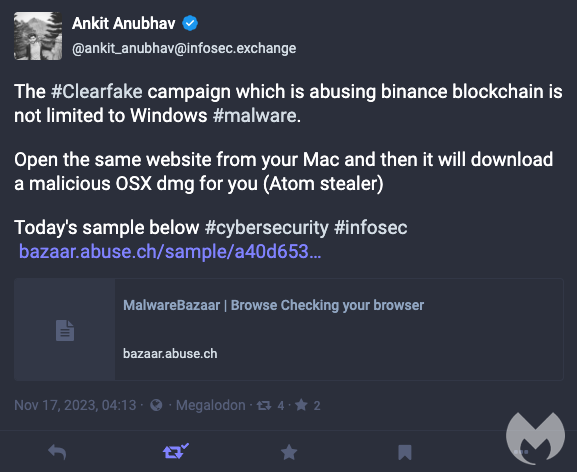
On November 17, security researcher Ankit Anubhav observed that ClearFake was distributed to Mac users as well with a corresponding payload:
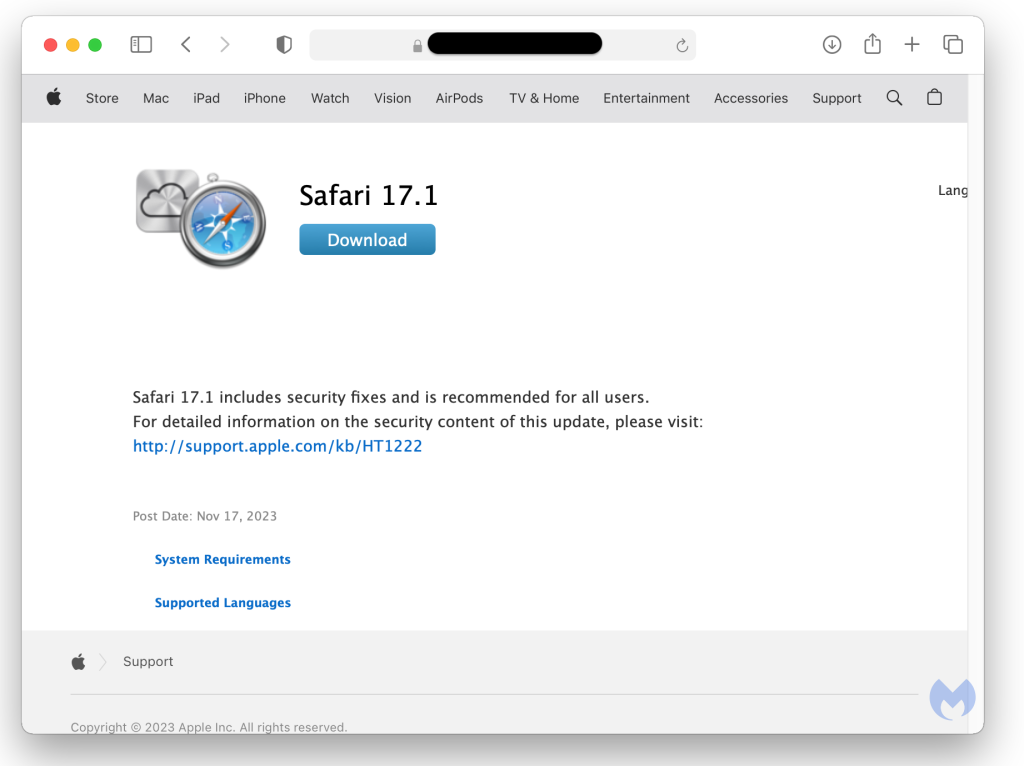
The Safari template mimics the official Apple website and is available in different languages:
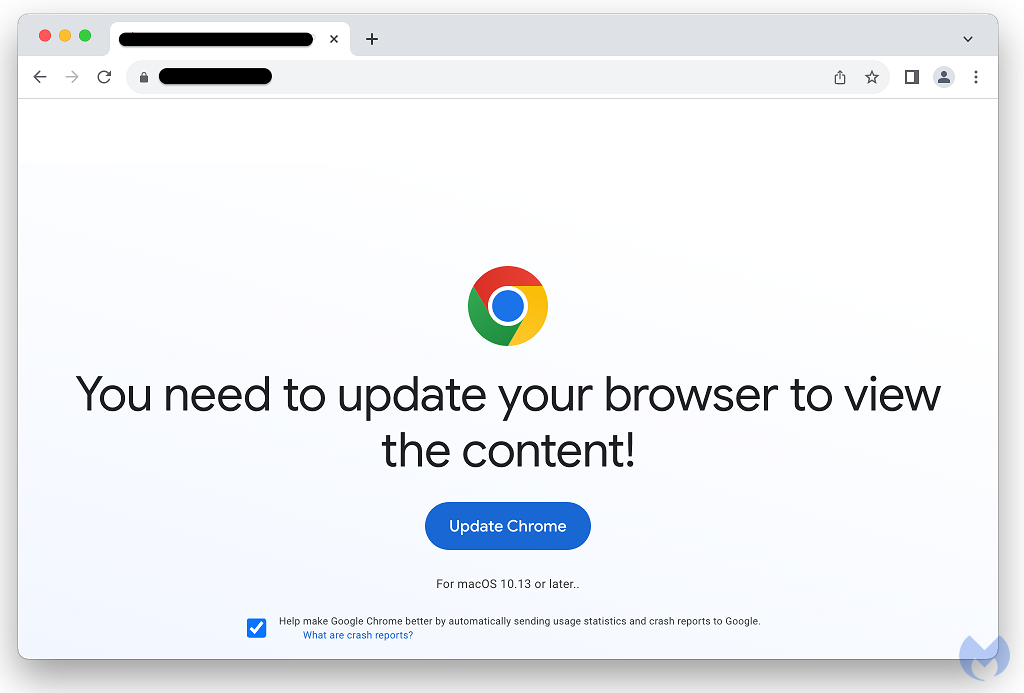
Since Google Chrome is also popular on Macs, there is a template for it which closely resembles the one used for Windows users:
Atomic Stealer
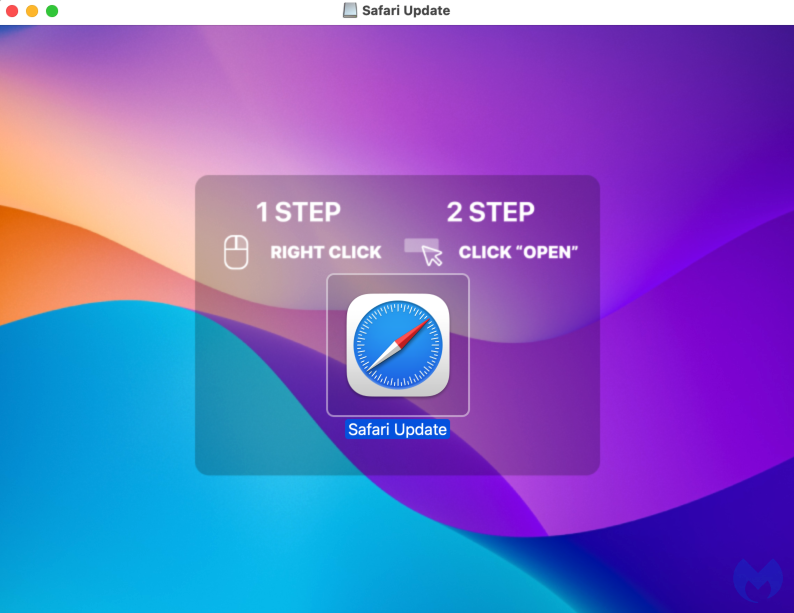
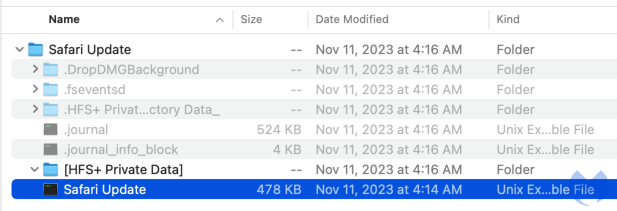
The payload is made for for Mac users, a DMG file purporting to be a Safari or Chrome update. Victims are instructed on how to open the file which immediately runs commands after prompting for the administrative password.
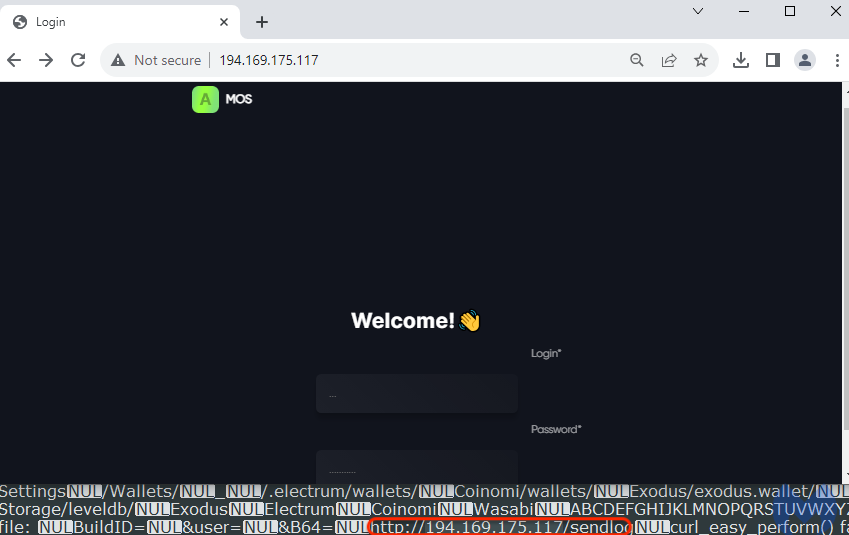
Looking at the strings from the malicious application, we can see those commands which include password and file grabbing capabilities:
find-generic-password -ga 'Chrome' | awk '{print $2}' SecKeychainSearchCopyNext: /Chromium/Chrome /Chromium/Chrome/Local State FileGrabber tell application "Finder" set desktopFolder to path to desktop folder set documentsFolder to path to documents folder set srcFiles to every file of desktopFolder whose name extension is in {"txt", "rtf", "doc", "docx", "xls", "key", "wallet", "jpg", "png", "web3", "dat"} set docsFiles to every file of documentsFolder whose name extension is in {"txt", "rtf", "doc", "docx", "xls", "key", "wallet", "jpg", "png", "web3", "dat"}In the same file, we can find the malware’s command and control server where the stolen data is sent to:
Macs need protection too
Fake browser updates have been a common theme for Windows users for years, and yet up until now the threat actors didn’t expand onto MacOS in a consistent way. The popularity of stealers such as AMOS makes it quite easy to adapt the payload to different victims, with minor adjustments.
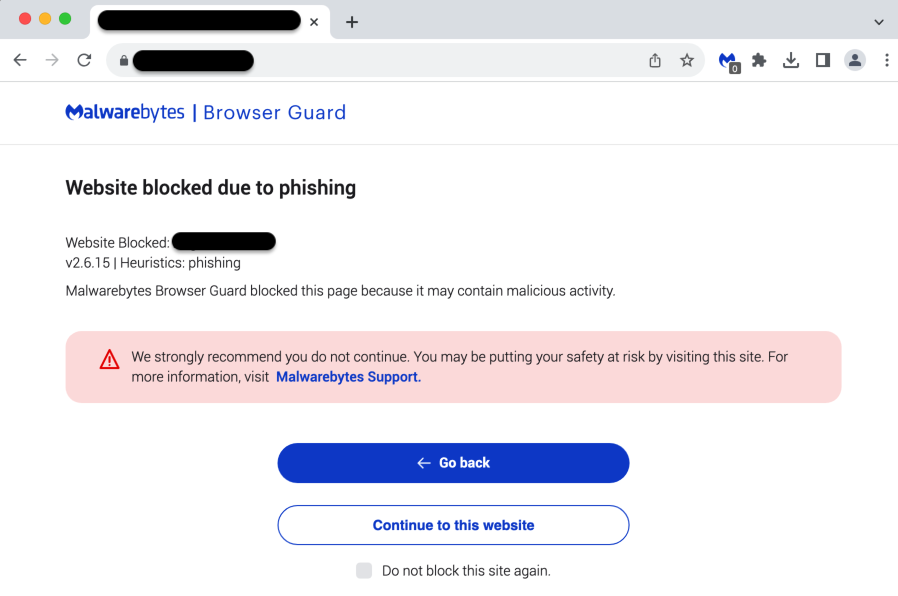
Because ClearFake has become one of the main social engineering campaigns recently, Mac users should pay particular attention to it. We recommend leveraging web protection tools to block the malicious infrastructure associated with this threat actor.
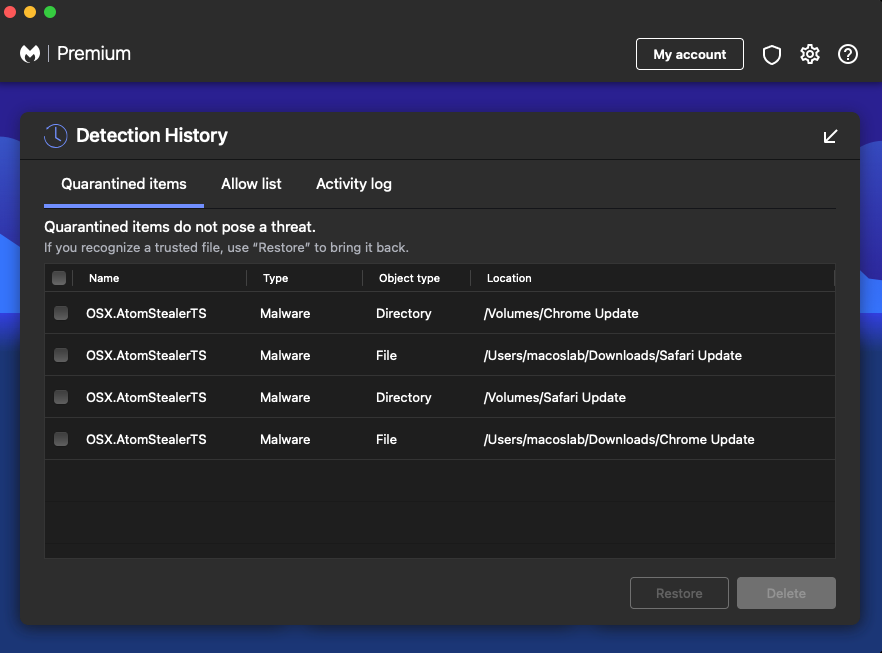
Malwarebytes users are protected against Atomic Stealer:
Indicators of Compromise
Malicious domains
longlakeweb[.]com chalomannoakhali[.]com jaminzaidad[.]com royaltrustrbc[.]com
AMOS stealer
4cb531bd83a1ebf4061c98f799cdc2922059aff1a49939d427054a556e89f464
be634e786d5d01b91f46efd63e8d71f79b423bfb2d23459e5060a9532b4dcc7b
AMOS C2
194.169.175[.]117